In this Microsoft Entra ID and Microsoft 365, we will show how to disable SMS authentication as a 2nd factor.
As Multifactor authentication has become popular, so have scams that trick users into giving SMS codes and gaining unauthorized access to Microsoft 365 and Entra ID.
This post will focus on the steps you need to take to disable SMS as an authenticator option.
Disable SMS Verification and Authentication
Follow these steps to stop users from registering SMS as an MFA solution. Open the Microsoft Entra ID console.
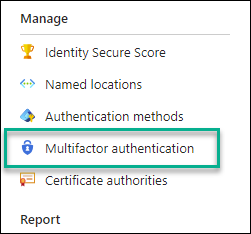
Click on Security
Click on Multifactor authentication
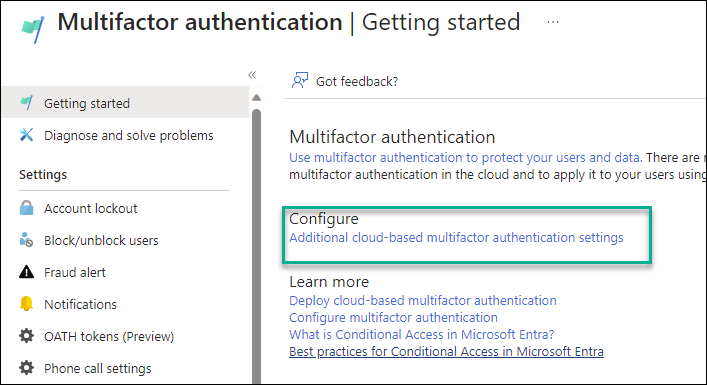
From the Multifactor authentication page, click on Additional cloud-based multifactor authentication settings.
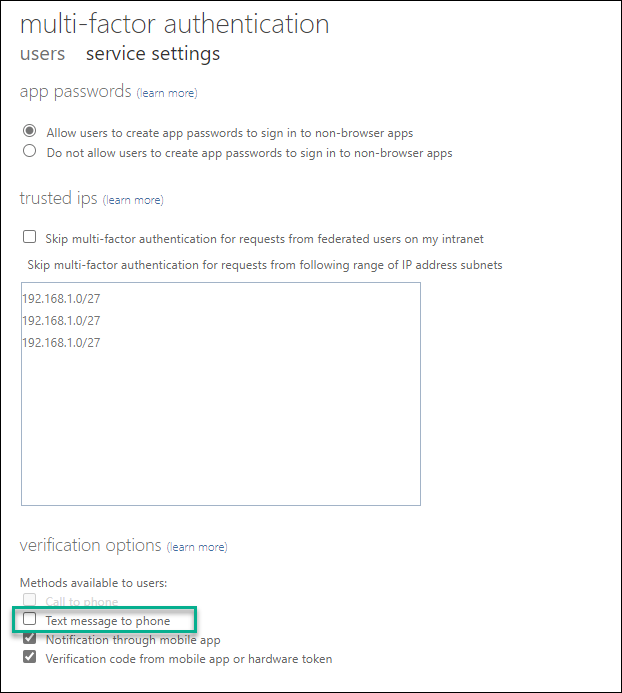
From the Authentication settings page, Untick “Text message to phone.“
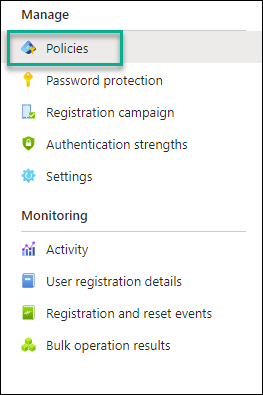
Return to the Microsoft Entra ID -> Security and click Authentication Methods.
Click on Policies
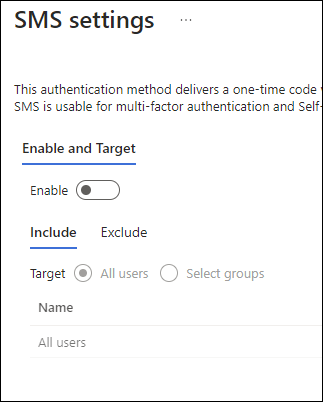
Click on SMS
Set the Enable to off
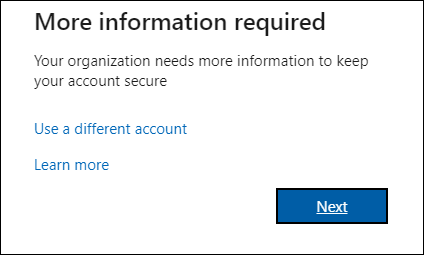
To test that the policy is working and SMS is disabled, I have a test user with whom I will sign in to Microsoft 365 for the first time.
When the user logs in for the first time, they will get the following message.
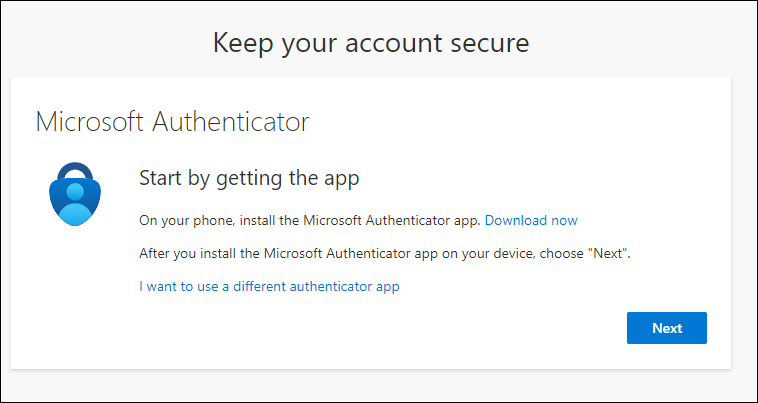
The next screen will only present the Microsoft Authenticator as an authentication method.
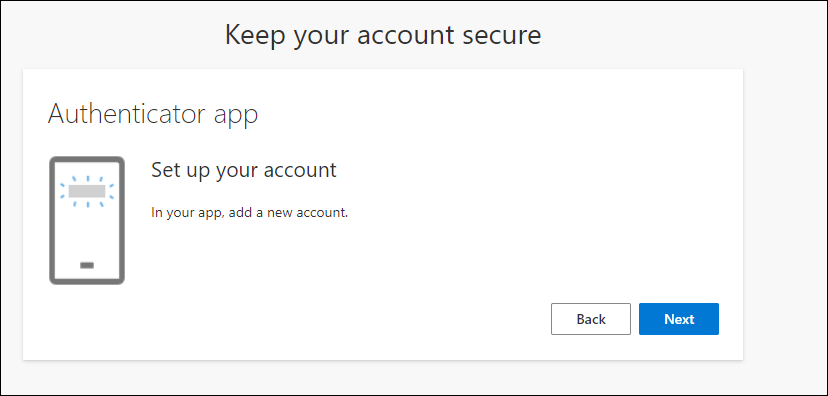
When they click “I want to use a different authenticator app, ” they will see the following message:
Before you roll this out to all your users, make sure you exclude a few admin accounts from MFA so you won’t get locked out of your tenant.