This blog post will show how to connect from Postman to Microsoft Azure Graph API and programmatically access Microsoft 365 and Azure resources.
Microsoft Graph API allows us to manage almost any Microsoft 365 and Azure Services using API calls. We can create, view, modify and delete resources with the API.
This blog post continues from our previous article, Create App Registration using Azure CLI and to complete this lab, you will need to create an App Registration first either using Azure CLI or the portal.
Generate Client Secret
Once our App Registration is configured with the correct permissions, we need to generate an App Secret. Below I have an Azure CLI command that will generate an App Secret.
az ad app credential reset --id APPIDPostman Configuration
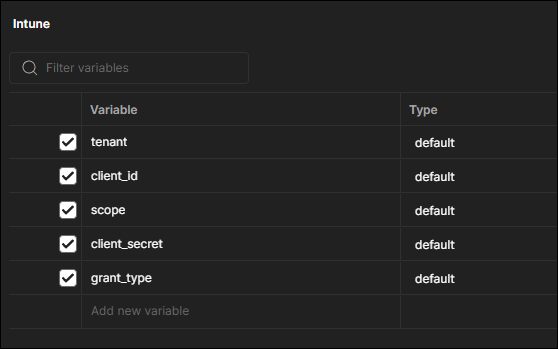
To get Postman to work and connect successfully to Grap API, we need to add the following parameters to Postman. In our case, we added them to the environment.
- tenant
- client_id
- scope
- client_secret
- grant_type
Create Token
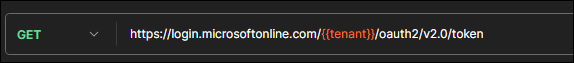
With the above environment parameters loaded into Postman, we need to generate a security token from Azure. The security token holds all the information about the permissions the app has and used to authorise the requests coming from Postman.
To generate a token we are going to use the following GET API call
https://login.microsoftonline.com/{{tenant}}/oauth2/v2.0/tokenYou can review the screenshot below
The output will look like
"token_type": "Bearer",
"expires_in": 3599,
"ext_expires_in": 3599,
"access_token": "Token shows here"
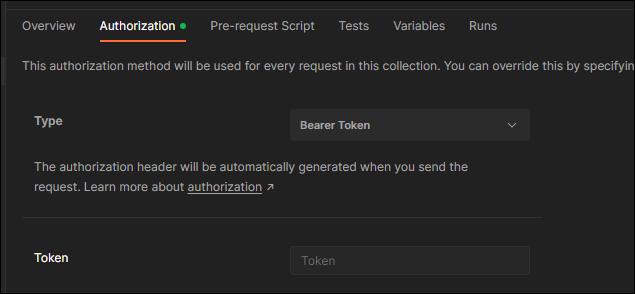
Copy the token hash and let’s add it to Postman. You can add it at the collection level under the Autorization tab or under each request.
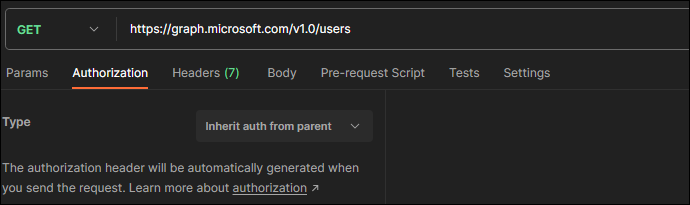
Create a Graph API Request
To create a Graph API request, We can use the API reference , In the example below I will get a list of all the Azure AD users.
https://graph.microsoft.com/v1.0/usersIn Postman the request looks like this: