In this blog post, I’ll show you how to enable password replication on Windows Server 2016 Read-Only Domain Controller.
Step By Step Guide
By default, Windows Server 2016 Read-Only Domain Controller doesn’t store password information or passwords.
When a user logs in to the network the Read-Only Domain Controller will pass the request to a writable Domain Controller to auth the user.
This process is not ideal and defeats the purpose of the Read-Only Domain Controller because you still heavily smash the network for authentication.
Because of that, Read-Only Domain Controllers offers us the option to replicate passwords and I will show you how.
Enable Password Replication
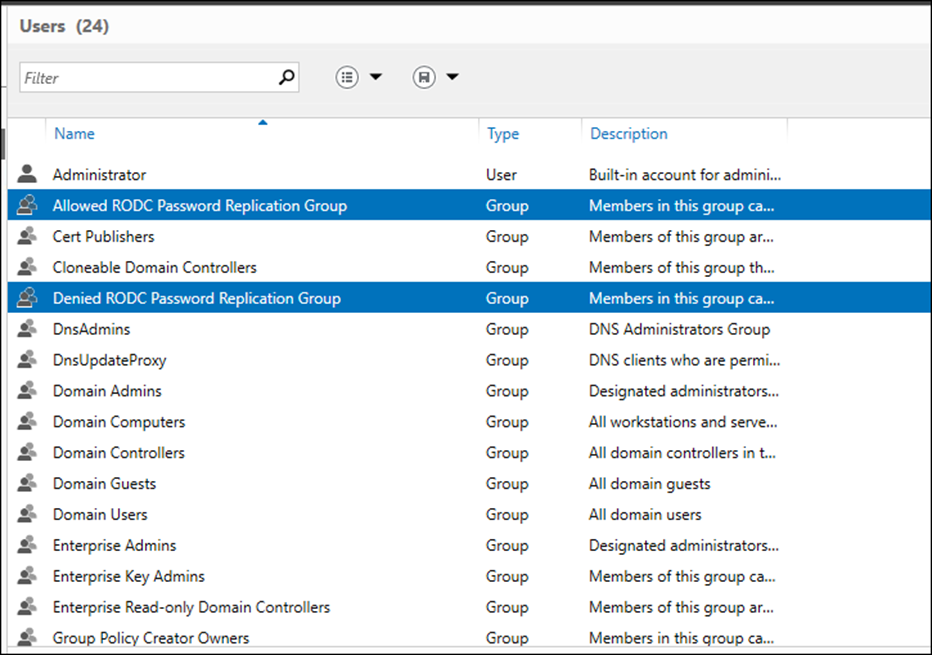
To enable, Password replication Microsoft made available two built-in groups In Active Directory.
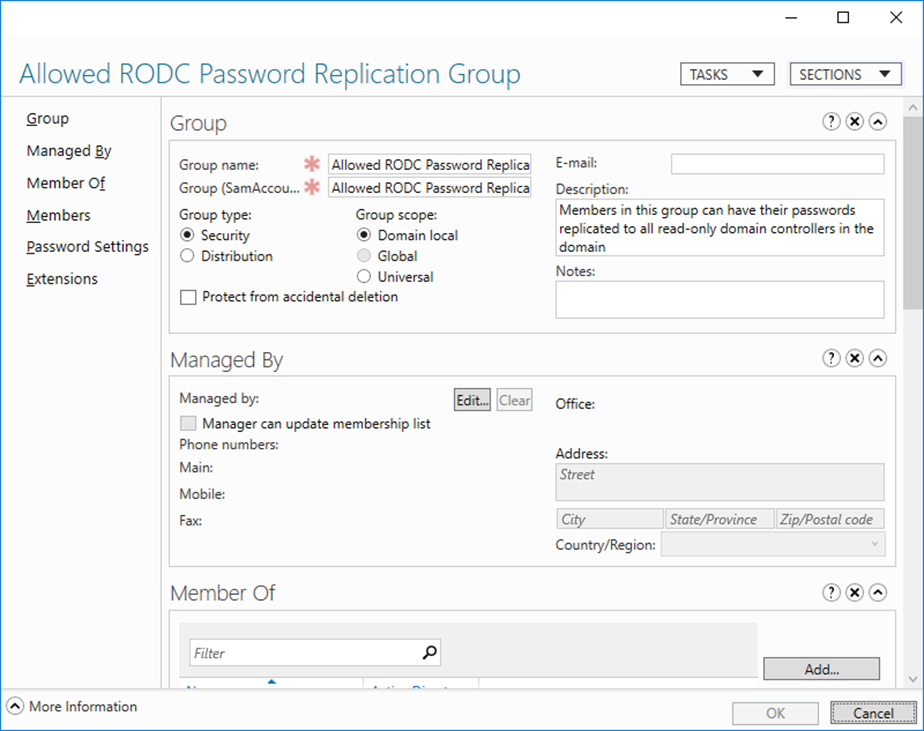
- Allowed RODC Password Replication Group
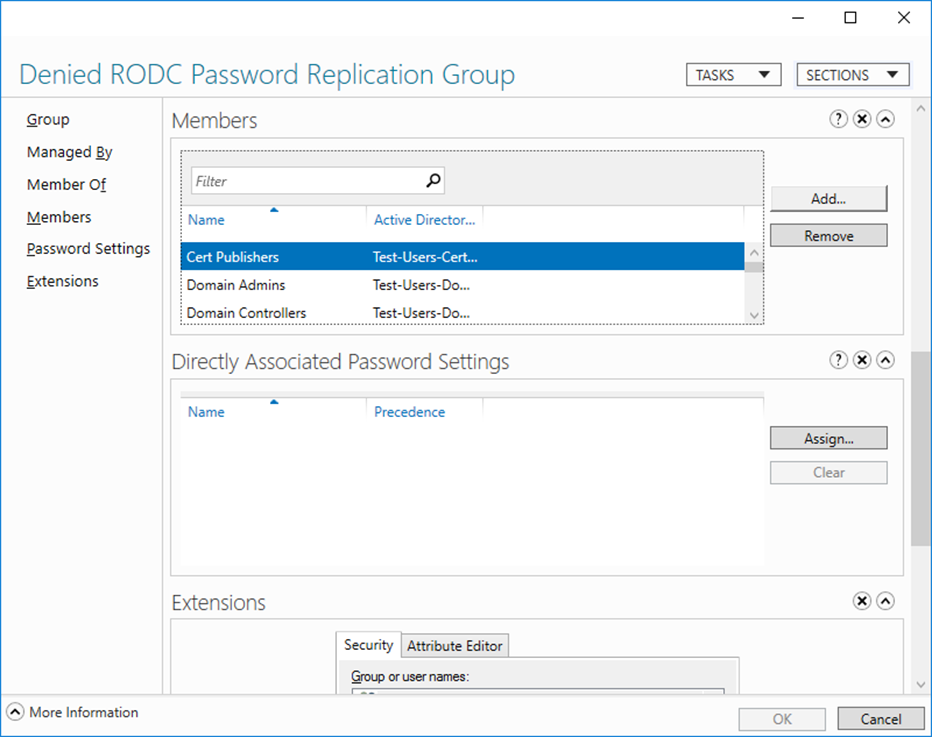
- Denied RODC Password Replication Group
If I want to allow password replication all I need to do Is add my users to the Allowed RODC Password Replication Group
By default, no one is a member of the group.
Also, The Denied RODC Password Replication Group holds users that you are denied explicitly and If you want to replicate their password you will need to remove them from the group and add them to the allowed Group.
About Read-Only Domain Controllers
A read-only domain controller (RODC) was first released with Windows Server 2008 and the Idea behind it that it allows us to deploy a DC in remote sites where physical security is ideal.
RODC hosts a read-only copy of our Active Directory Database which no one can modify if the server becomes unsecure.
Benefits
- Faster login times on remote sites
- Gives secure access to resources on the network
- Secure ADDS on remote sites
Limitation
- We can only install one Read-Only Domain Controller per AD Site and per Domain.
- A Domain Admin needs to run the Installation or a Delegated Administrator Account.
By default, RODS does not store passwords.