In this blog post, we will continue with the configuration of the access layer to Azure Virtual Desktop using Azure AD authentication.
Please visit the links below for the previous two blog posts in the series.
- Deploy Azure Virtual Desktop With Azure Active Directory Auth – Part 1
In part 2 of this series, we stopped after configuring our Azure AD Groups to access the AVD Application Groups. Now it is time to configure RBAC role assignment via IAM and configure RDP properties.
Configure Role Assignments
We need to configure role assignments using the Azure RBAC policy to access Azure AD domain joined machines using Azure AD credentials.
To configure RBA policy, Open the Azure portal
Click on Virtual Machines
Locate the AVD VM or VMs
Click on Access Control (AIM)
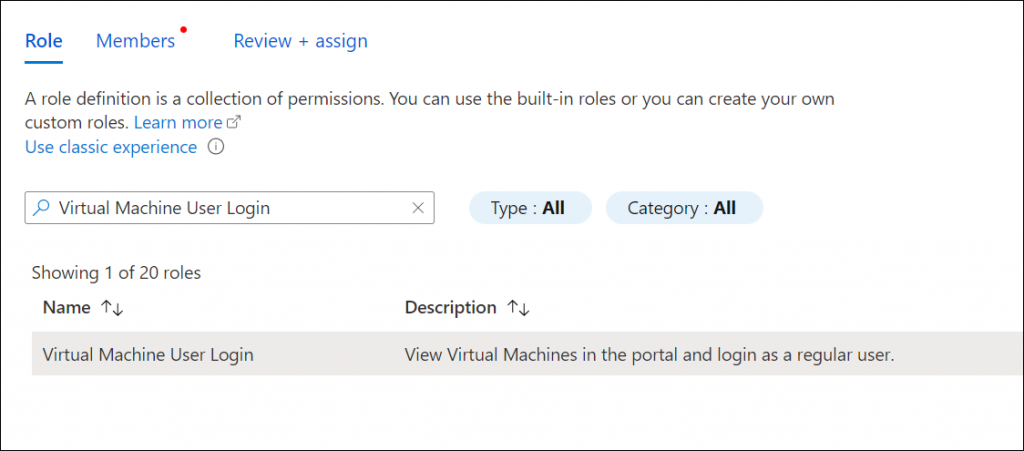
Click Add -> Add role assignment

Using the Role assignment, add the following two roles
- Virtual Machine User Login
- Virtual Machine Administrator Login
When you add the roles, add the Azure Groups we created in Part 1 (AVD Users, AVD Admins ) as the members and make sure you map them accordingly (Users to Users Admins to Admins)
In the upcoming and last post of this series, we will configure the RDP properties of our AVD pool to allow access to AVD.