In this blog post, I will show you how I enable and configure BitLocker Encryption on a joined Azure AD device with Microsoft Intune using a configuration policy.
Device Encryption can add an extra data protection capability to any organization regardless of the data type stored on the disk.
About BitLocker
BitLocker Drive Encryption is used to encrypt NTFS volumes on a Windows Device and protect the device from data theft if the device is comprised.
Specifically, it’s good in cases where the disk drive is removed from a stolen machine and connected to another machine.
BitLocker is using a TPM hardware chip that detects if the disk was tampered while offline.
Requirements
BitLocker is not available on Windows 10 Home edition so make sure your machine is running Pro or enterprise edition.
Configuration Policy
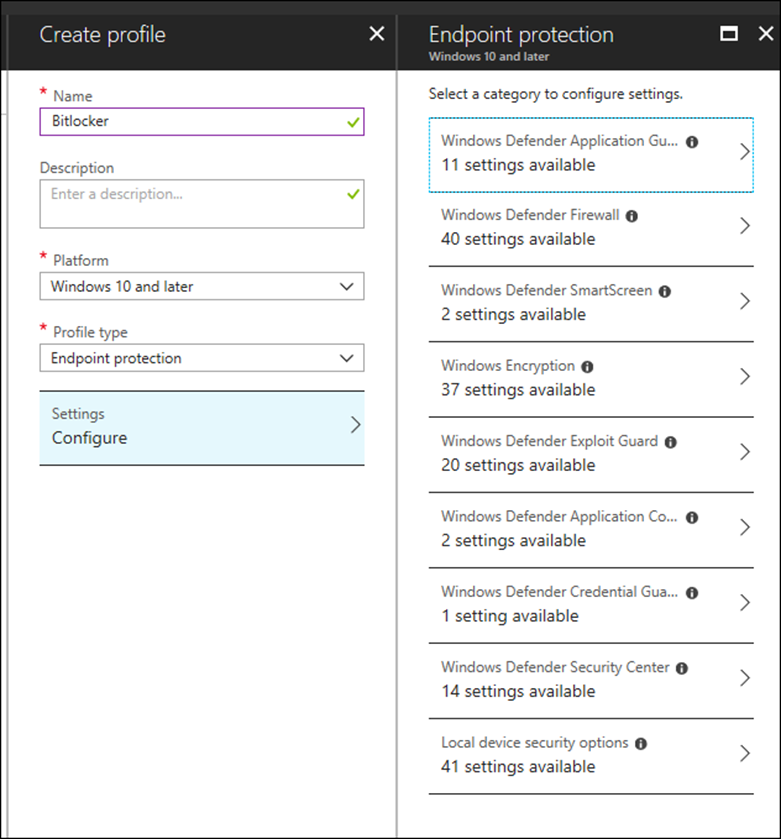
Below, I will start the process of creating a configuration policy that will enable BitLocker by going to Intune -> Configuration Policy – > Create Policy
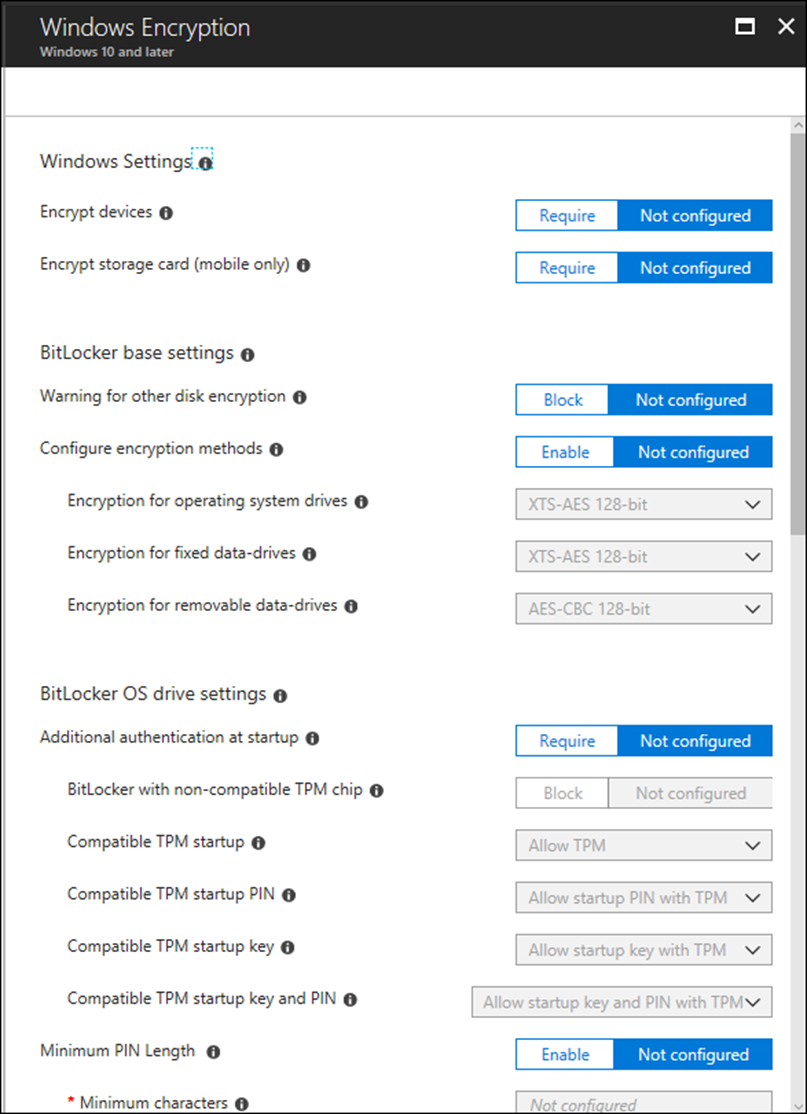
I will select Endpoint protection -> Windows Encryption, As you can see below Intune offers 37 settings option for BitLocker
Below, I will switch on the needed options
Assignment Policy
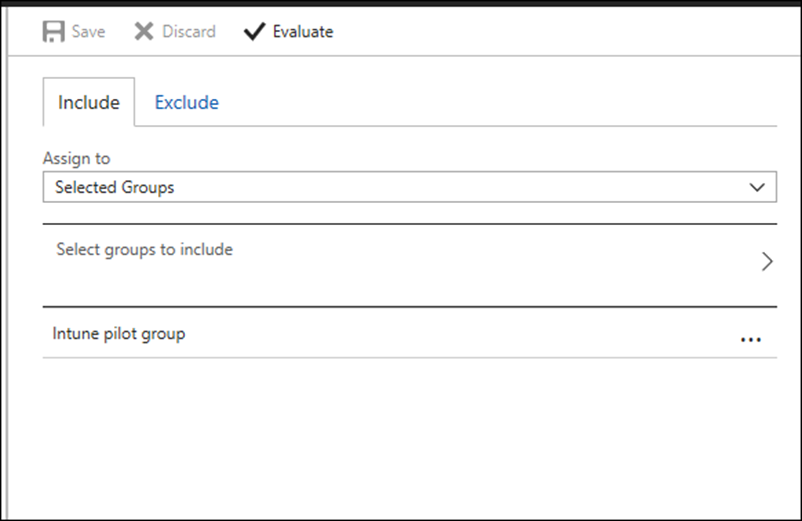
After setting the policy, I will go ahead and assign the policy to my Pilot group for testing
Encryption in Action
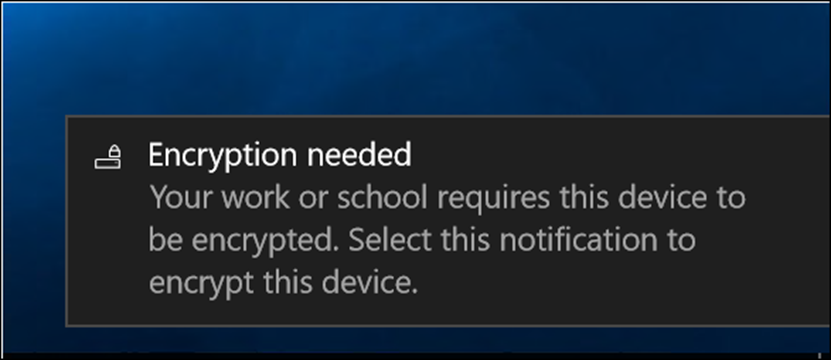
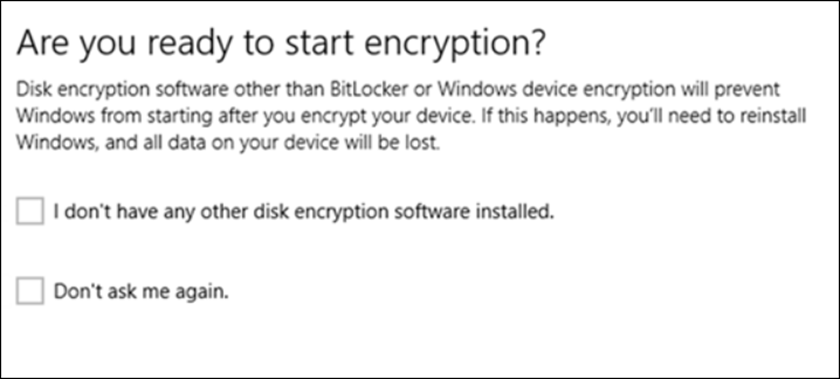
After login to my Windows 10 machine, Windows will display the message below telling me that I need to encrypt my device
I will answer the questions and click next
Windows now will start the encryption process

Microsoft Intune
Intune is a cloud-based Mobile Device Management solution from Microsoft that allows us to protect and manage mobile devices as a full corporate device or as BYOD devices.
Microsoft Intune is also part of Microsoft’s Enterprise Mobility + Security (EMS) suite that includes Azure Active Directory and Azure Active Directory Information Protection.
