In this blog post, I will show you how to block legacy authentication to Office 365 using Azure Active Directory Conditional Access feature.
Azure AD Conditional Access
Conditional Access is P1 feature in Azure AD that allows us to control which users, devices and applications are allowed, or not allowed to log in to
and with which method they will use to log in (Password or MFA).
Before you start
Make sure you apply the policy to a small number of users before using it to all users.
You need to have an Azure AD P1 license to use Conditional Access.
Crete a Conditional Access Policy
To create a rule, Click on Conditional Access and New policy

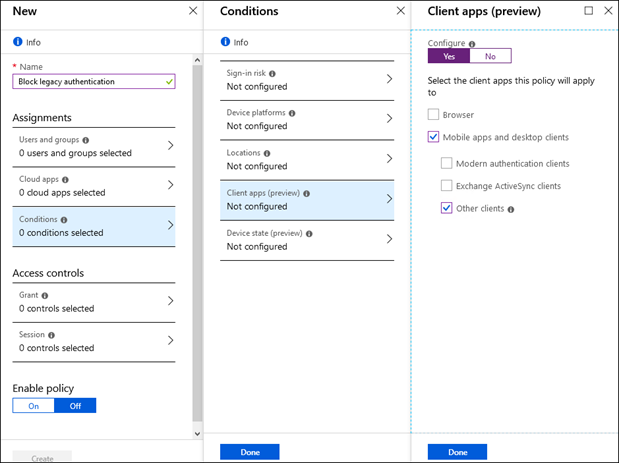
I name the policy and selected users to it fromthe Users and Groups section.

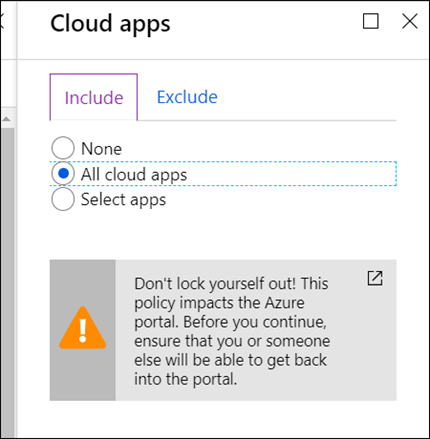
From the Cloud Apps section select All cloud apps
From the Conditions section I click on Client apps (Preview).
In the Client Apps page, I select Yes, and tick Mobile apps and desktop clients and Other clients.
Click done to finish.
From the Access controls section click on Grant and use the Block access option.
Click select.

In the Enable policy click On and Create.

A Conditional Access policy takes a few hours to apply to users fully, so monitor the rule and the users for a few days before using to All Users.