In this blog post, I’ll show you how to auto-enroll and renew certificates for users and computers In Active Directory using Group Policy and Enterprise CA.
Certificate Autoenrollment
When using Enterprise CA In a Domain environment we have the choice to automate the entire process of enrolling and renew certificates using group policy.
Requirements
To get this done, I’ll need to have:
- The certificate template needs to be configured for Windows Server 2008 and above compatibility.
- Enterprise Certificate Authority
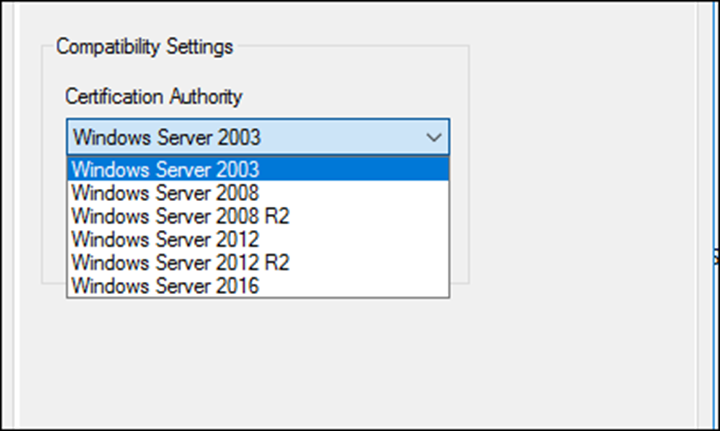
To get started, I’ll configure my Certificate to use Windows Server 2016 compatibility level.
My recommendation Is not to change the original certificate template but to duplicate it and work on the new one.
Duplicate Certificate Template
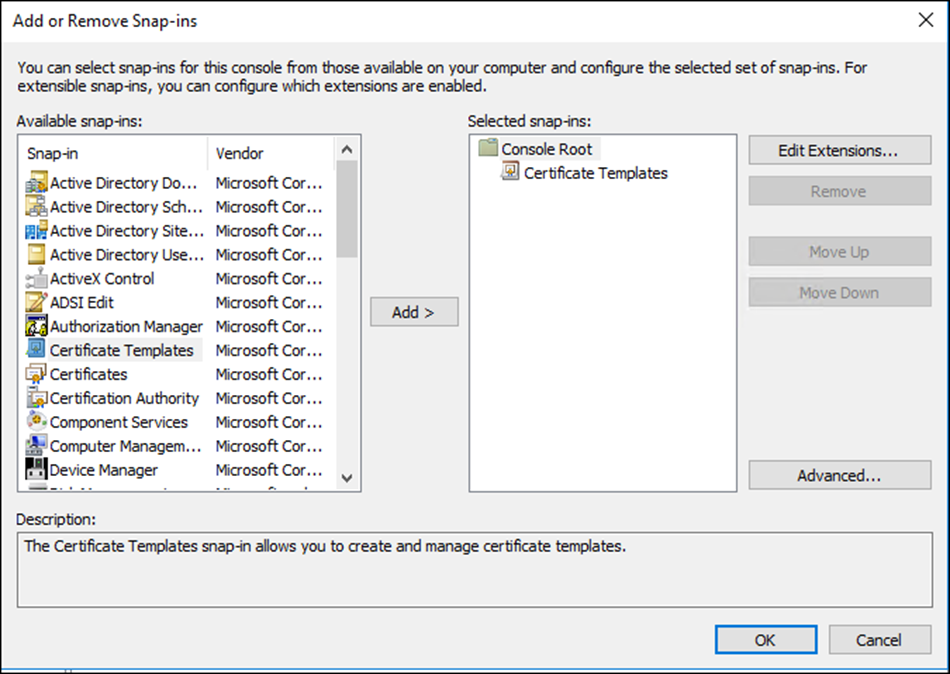
To duplicate my certificate and change the compatibility level, I’ll open the Certificate Template MMC
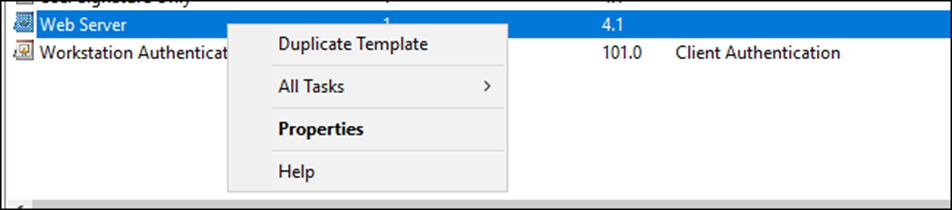
I’ll locate the template, I’ll use for autoenrollment -> Right Click and Duplicate Template
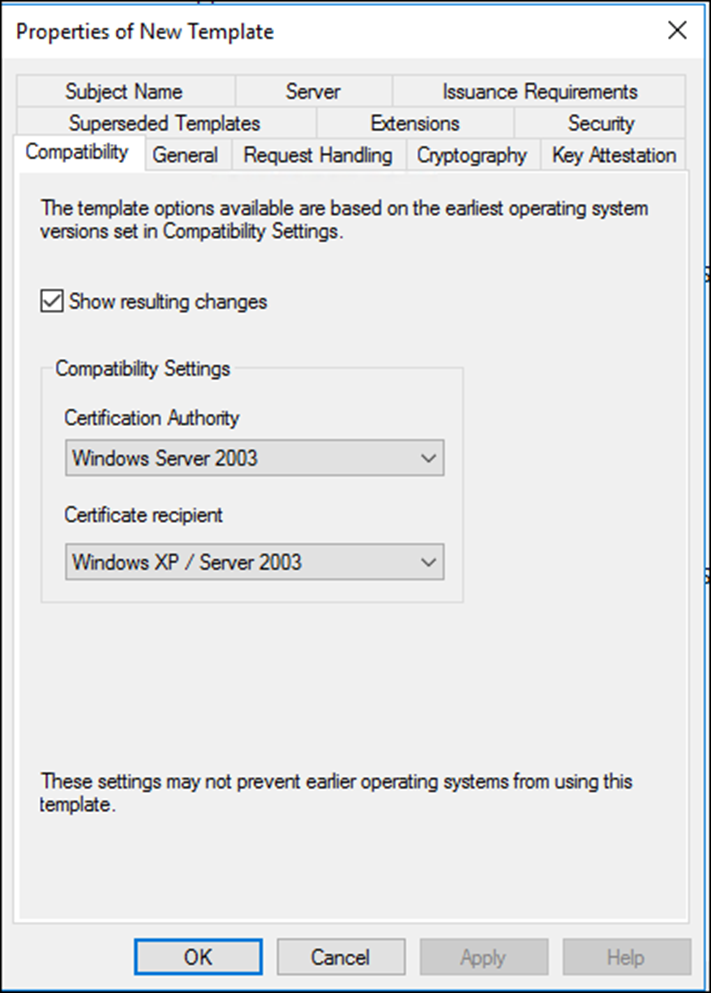
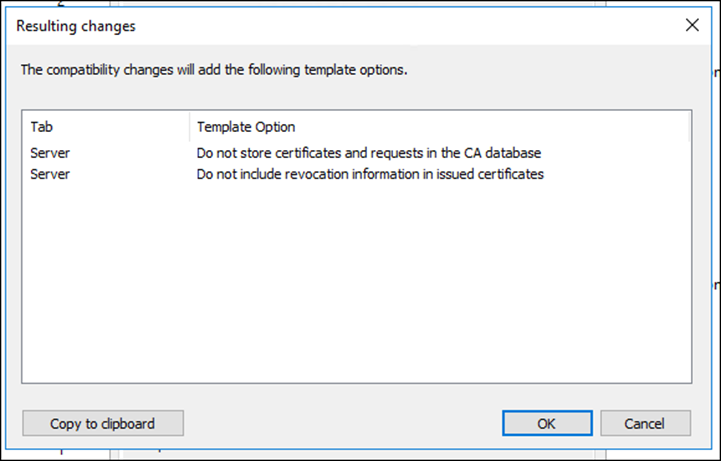
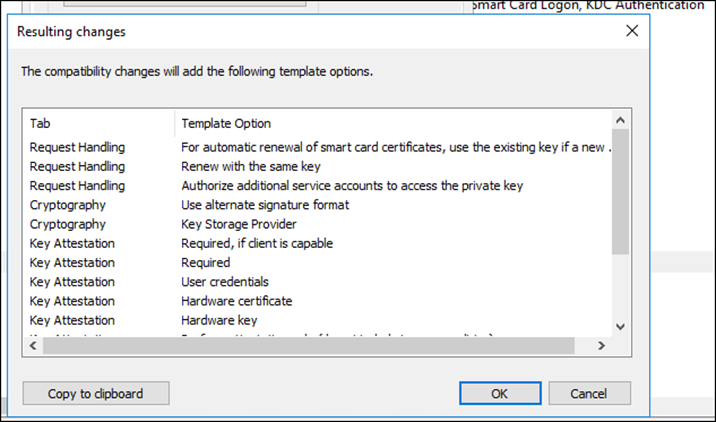
From the Compatibility tab, I’ll change the Compatibility level
In my case, I’m selecting Windows Server 2016
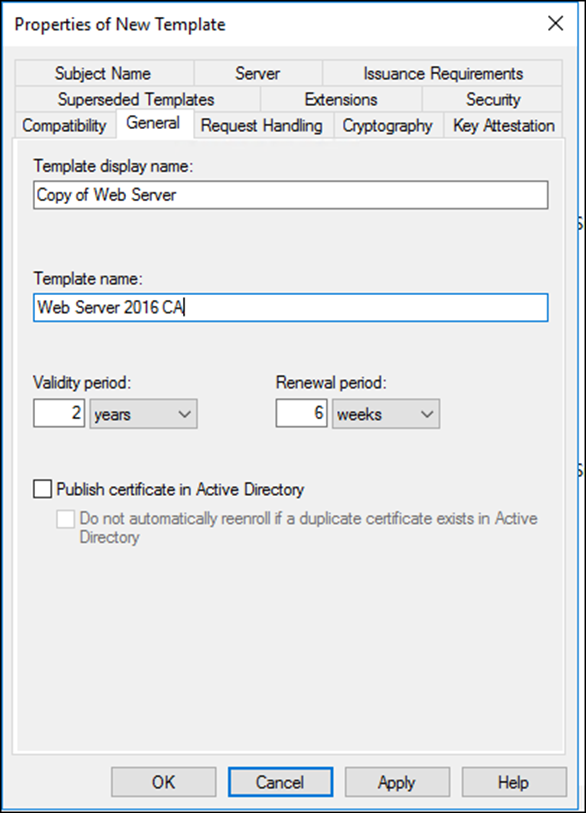
I’ll also, change the template Display and Template name
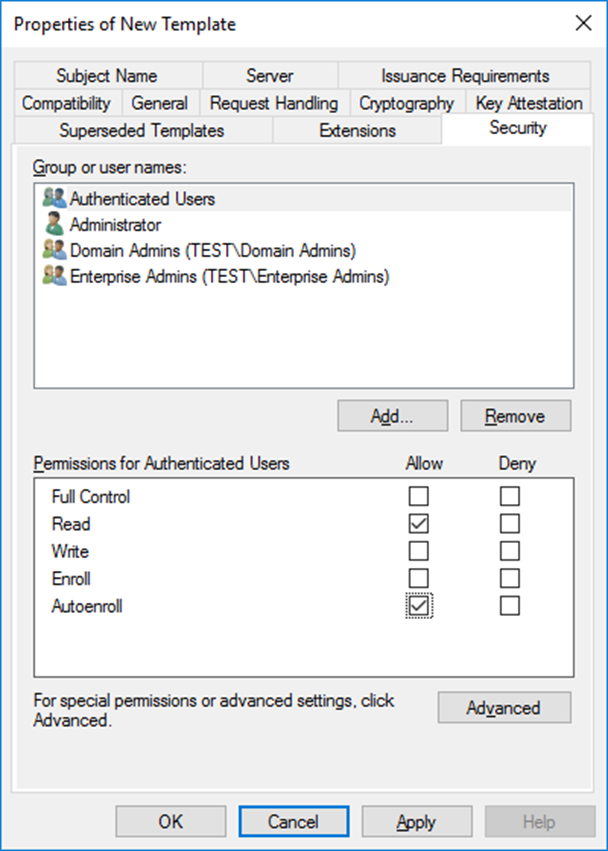
Autoenrollment permissions
And the most important part, I’ll give my Domain users Autoenroll permissions.
From the new certificate properties ->Security tab I’ll select my Domain Users and give them Autoenroll.
Group Policy Settings
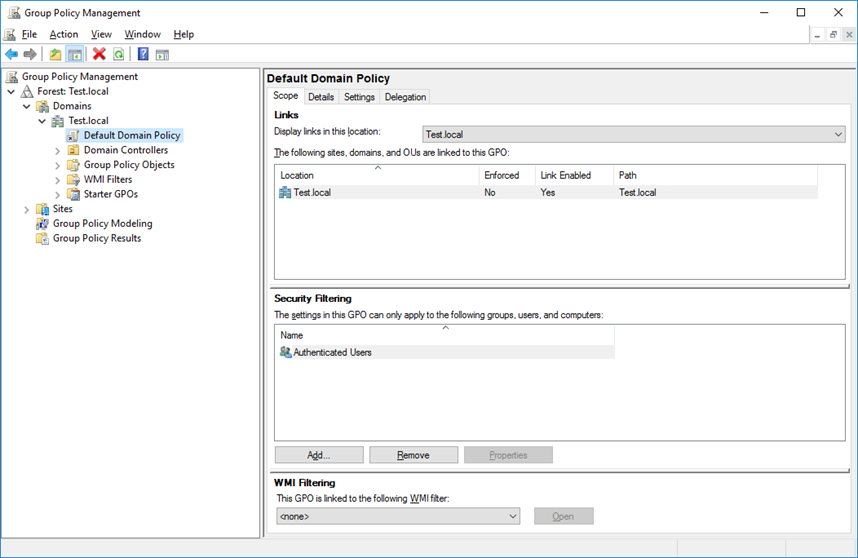
Now, I’ll configure Group Policy to enable autoenrollment, From the Group Policy Management Console I’ll edit my GPO
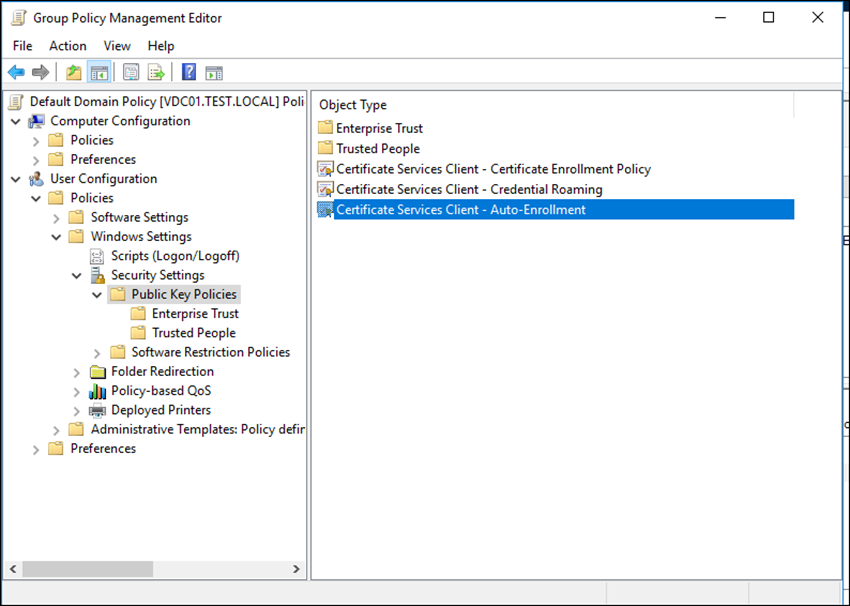
For users I’ll modify the settings under:
User Configuration -> Policies -> Security Settings -> Public Key Policies
For computer use the computer configuration -> Policies -> Security Settings -> Public Key Policies
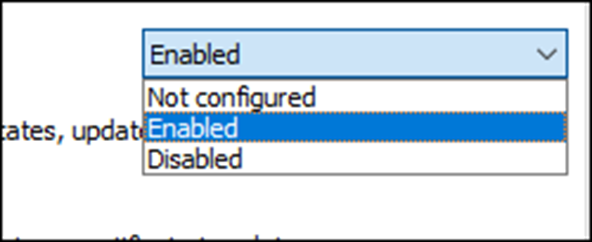
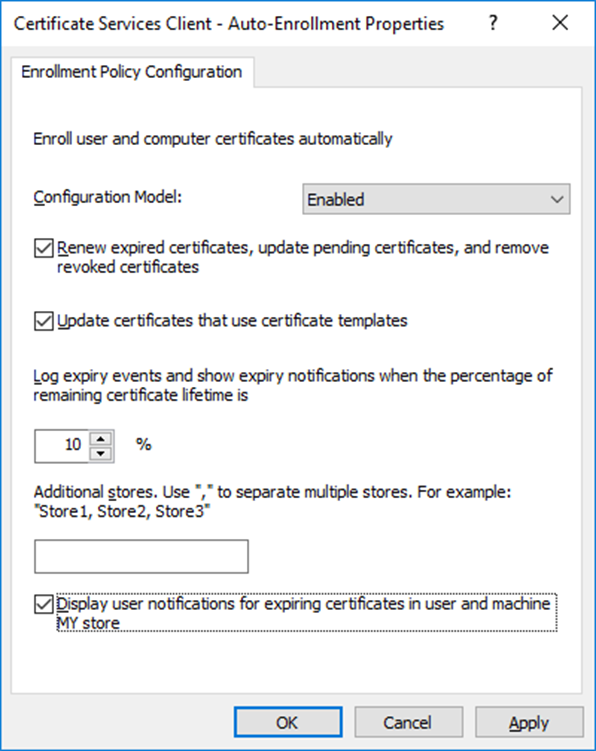
In the Configuration Mode, I’ll use enabled
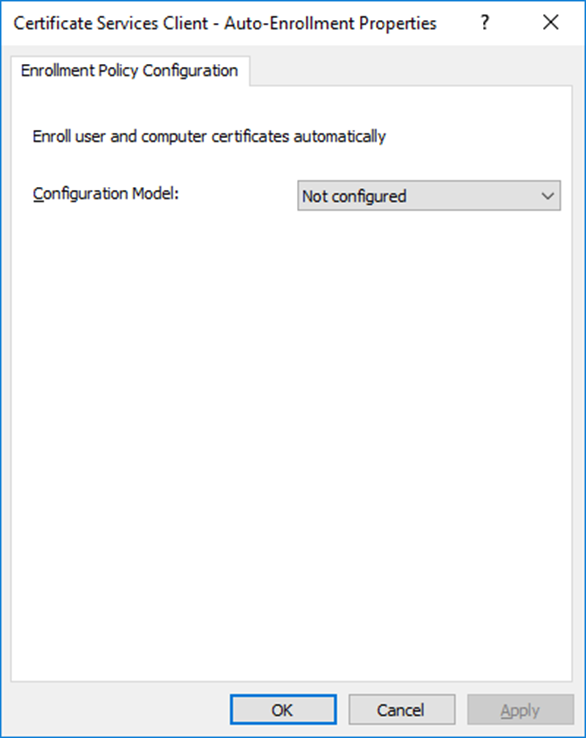
Next, I’ll use the settings below.
Conclusion
Group Policy Autoenrollment is a quick win In enterprise environments where automation Is the key to a successful management.